- User ID
- 1
- Joined
- 7 Jan 2019
- Messages
- 1,547
- Reaction score
- 126
- Points
- 63
Hi @Hav0c,Hello there,
So after reading 1, 2, 3, 4, 5 and this article and something keeps blocking me
Below the code that I used
Code:/ip pool add name=vpn-pool ranges=192.168.1.15-192.168.1.20 /ppp profile add name=ipsec_vpn local-address=192.168.1.254 remote-address=vpn-pool dns-server=192.168.1.254 /interface l2tp-server server set enabled=yes authentication=mschap1,mschap2,chap default-profile=ipsec_vpn use-ipsec=yes /ip ipsec policy set [ find default=yes ] src-address=0.0.0.0/0 dst-address=0.0.0.0/0 protocol=all proposal=default template=yes /ip ipsec peer add exchange-mode=main passive=yes name=l2tpserver /ip ipsec identity add generate-policy=port-override auth-method=pre-shared-key secret=<SUPPERSECUREPASSWORD> peer=l2tpserver /ip ipsec proposal set default auth-algorithms=sha1 enc-algorithms=aes-128-cdc,aes-256-cdc,aes-128-ctr pfs-group=modp1024 /ppp secret add name=<YOURVPNNAME> password=<YOURVPNPASSWORD> service=l2tp profile=ipsec_vpn /ip firewall filter add action=accept chain=input protocol=ipsec-esp comment="Allow L2TP VPN (ipsec-esp)" /ip firewall filter add action=accept chain=input protocol=udp dst-port=500,1701,4500 comment="Allow L2TP VPN (500,4500,1701/udp)"
This article code
Code:/interface l2tp-server server set enabled=yes use-ipsec=required ipsec-secret=<SUPPERSECUREPASSWORD> /ip pool add name=vpn_pool ranges=192.168.1.15-192.168.1.20 /ppp profile add name=ipsec_vpn local-address=192.168.1.254 remote-address=vpn_pool /ppp secret add name=<YOURVPNNAME> password=<YOURVPNPASSWORD> service=l2tp profile=ipsec_vpn /ip firewall filter add action=accept chain=input protocol=ipsec-esp comment="Allow L2TP VPN (ipsec-esp)" /ip firewall filter add action=accept chain=input protocol=udp dst-port=500,1701,4500 comment="Allow L2TP VPN (500,4500,1701/udp)"
RouterOS 6.45.6 (Stable)
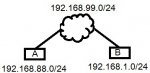
What happens is that the connection is made, the Client LOCAL ip is 192.168.88.2 and it gets the IP of 192.168.1.20 from the Remote Router the DNS is the Remote Routers IP of 192.168.1.254
When I do a tracert to the Remote Routers IP the trace works
When I do a tracert to the Remote Routers WAN IP the trace works
The Issue is that i cannot accesses anything on the Remote side...
Suggestions to look at ?
Can you ping 192.168.1.254 and see you get any response?
And also try to ping the other devices on the remote network.
Check if there's any other firewall rule that overrides the IPsec rules?